Introducing CWE-based Weaknesses

Letting go is hard.
Today we say goodbye to the original 18 vulnerability types on HackerOne. They’ve been with us since the very beginning.
Fortunately, we are moving on to bigger and better things.
We updated our vulnerability taxonomy to include a more complete weakness suite based on the industry-standard Common Weakness Enumeration (CWE). In this post we’ll go through the high level changes, why we chose CWE, and what it looks like.
What is CWE?
Common Weakness Enumeration (CWE) is a community-developed list of common software security weaknesses. It serves as a common language, a measuring stick for software security tools, and as a baseline for weakness identification, mitigation, and prevention efforts.
Benefits of Our Upgraded Weaknesses
Our extended weaknesses based on CWE provide a much more complete and accurate description of reported vulnerability, and more importantly, adopts a common language that is endorsed by the security community. We believe our alignment would greatly benefit all of our programs and hackers with:
- Reducing time and effort to triage, validate, and prioritize reports;
- Improving the alignment of expectations for report resolution and bounty payouts;
- Improving interoperability with external systems;
- Improving interoperability with custom internal taxonomies;
- Unlocking advanced analytics.
And more importantly, it helps put HackerOne in a pivotal position, as a service provider and a community, to engage in industry-wide discussion on how to eliminate and/or mitigate security weaknesses.
Upgraded Weaknesses In Action
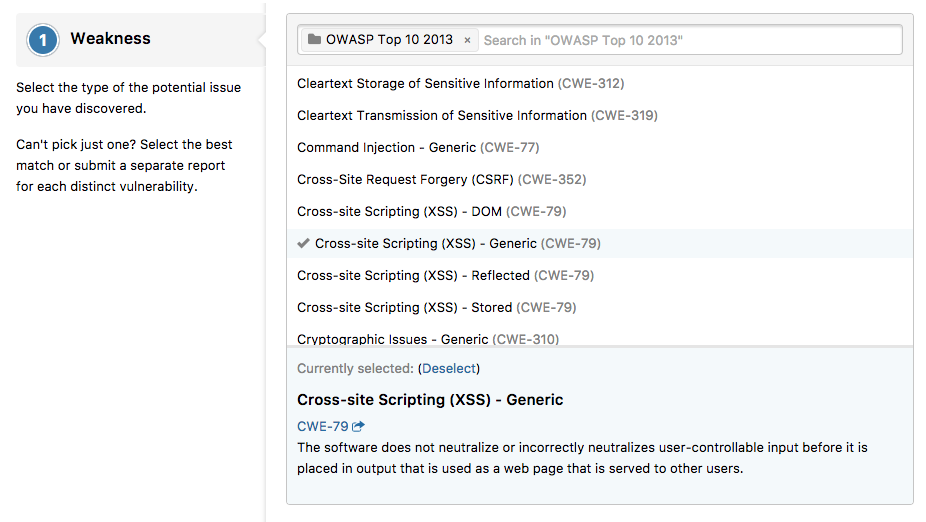
After many iterations, we have released a custom list of weakness types based primarily on CWE that provides comprehensive coverage and flexibility for security teams and hackers.
This list includes 100+ weaknesses adopted mostly from CWE, along with 20+ clusters. We introduced clusters as a way of classifying our now-extensive weakness list. Our cluster suite is easily mappable to external categories that are widely adopted in the security industry, including OWASP Top 10 2013 and OWASP Mobile Top 10 2016.
Our weaknesses are fully compatible with:
- Our legacy vulnerability types; see the full list and relationship to our legacy vulnerability types.
- Any external system that utilizes CWE, including Qualys, Coverity, Veracode, etc.
- Custom internal taxonomies based on CWE that any of our amazing customers have created.
The clusters and weaknesses are designed to be a living document that will evolve and update over time. Our team is committed to regular reviews to make sure they remain relevant in sync. And of course, if you have any questions or have a weakness or cluster you'd like to see included, please let us know!
Pro Tips
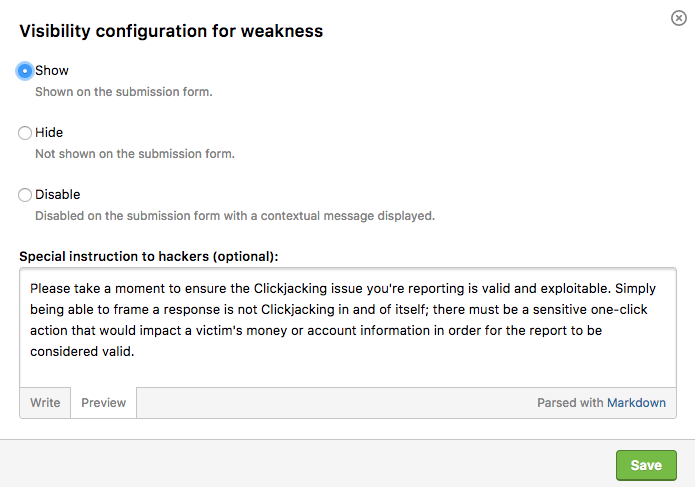
Hackers: Familiarize yourself with the new CWE types here. Programs: Head to your program settings to hide and/or disable unwanted weaknesses and add special instructions to hackers when needed.
For more of the nitty gritty details and the implications for hackers and security teams, see our help center article.
Special Thanks
We'd like to give a shout-out to The MITRE Corporation and the CWE sponsor US-CERT in the office of Cybersecurity and Communications at the U.S. Department of Homeland Security. Thank you for your support of this industry standard!
Stay Tuned for More
We love making new features and improving the platform. Share your feedback on the change! More updates are to come as we continue to build and expand upon our vulnerability taxonomy.
Brought to you by Pei, Sonya, Jens, Maarten, and Lars.
HackerOne is the #1 hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be criminally exploited. As the contemporary alternative to traditional penetration testing, our bug bounty program solutions encompass vulnerability assessment, crowdsourced testing and responsible disclosure management. Discover more about our security testing solutions or Contact Us today.
The 7th Annual Hacker-Powered Security Report
 Programs: Head to your program settings to hide and/or disable unwanted weaknesses and add special instructions to hackers when needed.
Programs: Head to your program settings to hide and/or disable unwanted weaknesses and add special instructions to hackers when needed.